
HTTP REQUEST SMUGGLING DESYNC ATTACK...
What is HTTP request smuggling. ? HTTP request smuggling is a technique that, allowing an attacker to bypass security controls,... Continue Reading
Installing Windows SubSystem For Linux
The Windows Subsystem for Linux (WSL) is a feature of windows operating system by which you can run a Linux... Continue Reading

Burp Suite Certificate Installation Android...
Android Nougat and above version is no longer trusts user supplied CA certificates. Then we need to install a trusted... Continue Reading
Windows 11 upgrade Insider Program
As we all Know the Microsoft has recently announced the windows next generation i.e. Windows 11 with the major GUI... Continue Reading
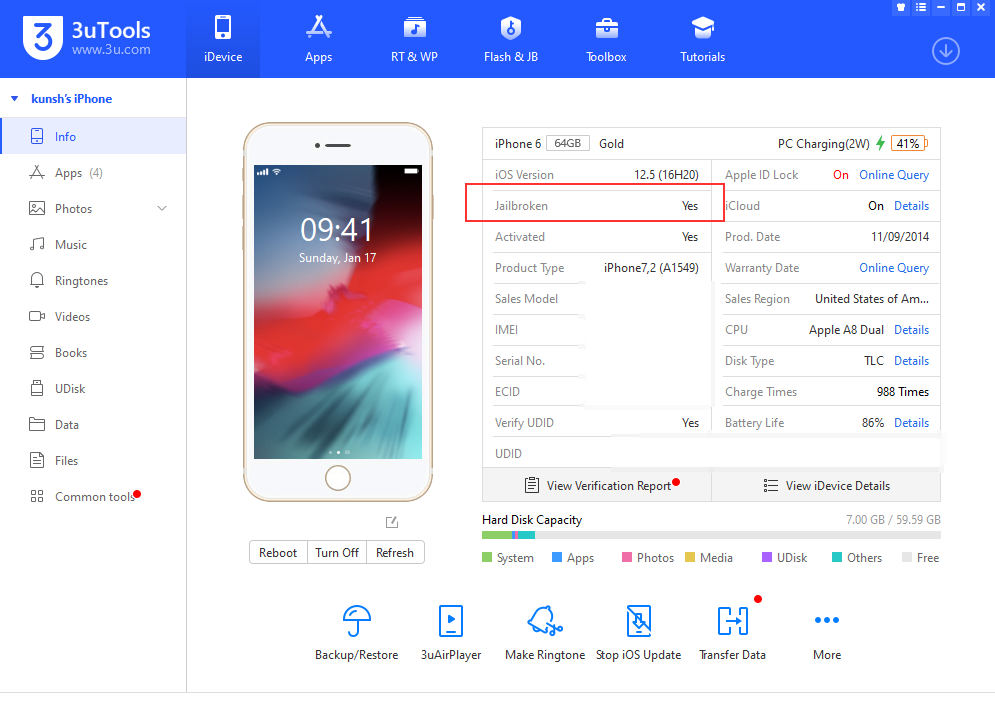
iOS Jailbreak and IPA installation...
3uTool is the all-in-one tool for iOS devices, we can jailbreak the device directly from 3utools, or either we can... Continue Reading
Code/Logic Breaking with Special Characters/Symbols.
Mostly Many developers while writing the code. They forgot to add regex for special characters/symbols which can break the flow/logic... Continue Reading

Web App Penetration Testing Checklist
The below are some common checklist for web application penetration testing. Information Gathering Spiders, Robots, and Crawlers Burpsuite crawler. Check... Continue Reading
Mobile application penetration testing, and...
Why penetration testing required? Mobile applications often process any sensitive data (like user details, accessing contacts, photos, etc.), which is... Continue Reading

Some Useful Commands for Ubuntu...
Below are the list of commands:- Commands Command usages and details $apropos Search Help manual pages (man -k) $apt-get... Continue Reading

Apache Security Headers Configuration.
Step 1:- Enable AllowOverride mode in config file. After successfully install the apache server open configuration file. The file location... Continue Reading

Android Root Detection Bypass via...
In this post, we will show you the basic steps of the root detection bypass method along with prevention implementation.... Continue Reading